Utilize Cloud Services for Enhanced Data Safety
Leveraging cloud services presents an engaging remedy for companies seeking to strengthen their information safety procedures. The concern occurs: how can the application of cloud solutions reinvent data security techniques and supply a robust guard versus prospective vulnerabilities?
Value of Cloud Safety
Ensuring durable cloud safety and security measures is extremely important in securing sensitive information in today's electronic landscape. As organizations increasingly rely upon cloud solutions to save and process their data, the demand for solid security methods can not be overstated. A violation in cloud safety and security can have extreme repercussions, varying from monetary losses to reputational damages.
One of the primary factors why cloud safety and security is essential is the common responsibility design employed by a lot of cloud service carriers. While the company is accountable for protecting the framework, customers are accountable for protecting their data within the cloud. This division of obligations emphasizes the significance of applying robust safety steps at the customer level.
Additionally, with the spreading of cyber threats targeting cloud atmospheres, such as ransomware and data breaches, organizations should remain aggressive and vigilant in mitigating threats. This entails on a regular basis upgrading safety and security procedures, checking for dubious activities, and informing staff members on ideal techniques for cloud security. By prioritizing cloud safety and security, organizations can much better protect their sensitive data and support the depend on of their stakeholders and consumers.
Information Security in the Cloud
Encryption in the cloud usually includes the use of cryptographic formulas to clamber information right into unreadable layouts. In addition, several cloud solution providers supply security devices to protect information at rest and in transit, enhancing overall data defense.
Secure Data Backup Solutions
Data backup remedies play a vital role in guaranteeing the durability and safety and security of data in the event of unexpected cases or information loss. Safe data backup solutions are important elements of a robust information safety technique. By frequently backing up information to protect cloud web servers, organizations can mitigate the threats connected with data loss due to cyber-attacks, equipment failures, or human error.
Implementing safe and secure information backup solutions entails choosing dependable cloud company that offer security, redundancy, and data honesty steps. Security makes sure that data remains safe and secure both in transportation and at remainder, securing it from unapproved gain access to. Redundancy devices such as data duplication throughout geographically dispersed servers aid avoid full data loss in instance of server failings or natural catastrophes. Additionally, data honesty checks ensure that the backed-up information continues to be unaltered and tamper-proof.
Organizations should develop computerized backup schedules to make sure that information is continually and efficiently backed up without hand-operated treatment. Normal screening of information restoration processes is also crucial to ensure the efficiency of the back-up options in recouping information when required. By spending in safe data backup services, companies can enhance their data security posture and reduce the impact of potential information breaches or disruptions.
Role of Access Controls
Implementing stringent accessibility controls is vital for preserving the security and stability of sensitive information within business systems. Gain access learn the facts here now to controls act as an important layer of defense versus unauthorized accessibility, guaranteeing that only accredited individuals can view or adjust delicate data. By specifying that can access details sources, organizations can restrict the danger of data violations and unapproved disclosures.
On a regular basis updating and reviewing access controls is necessary to adjust to business adjustments and advancing safety dangers. Continuous monitoring and bookkeeping of gain access to logs can help detect any type of questionable activities and unapproved access efforts without delay. Generally, robust view publisher site gain access to controls are essential in safeguarding delicate info and mitigating safety and security threats within business systems.
Compliance and Rules
Frequently guaranteeing compliance with relevant guidelines and criteria is necessary for companies to support data security and privacy actions. In the realm of cloud services, where data is often stored and refined on the surface, adherence to industry-specific regulations such as GDPR, HIPAA, or PCI DSS is important. universal cloud Service.
Many providers offer security abilities, access controls, and audit routes to assist organizations meet data security criteria. By leveraging compliant cloud solutions, companies can enhance their information safety and security posture while fulfilling governing commitments.
Final Thought
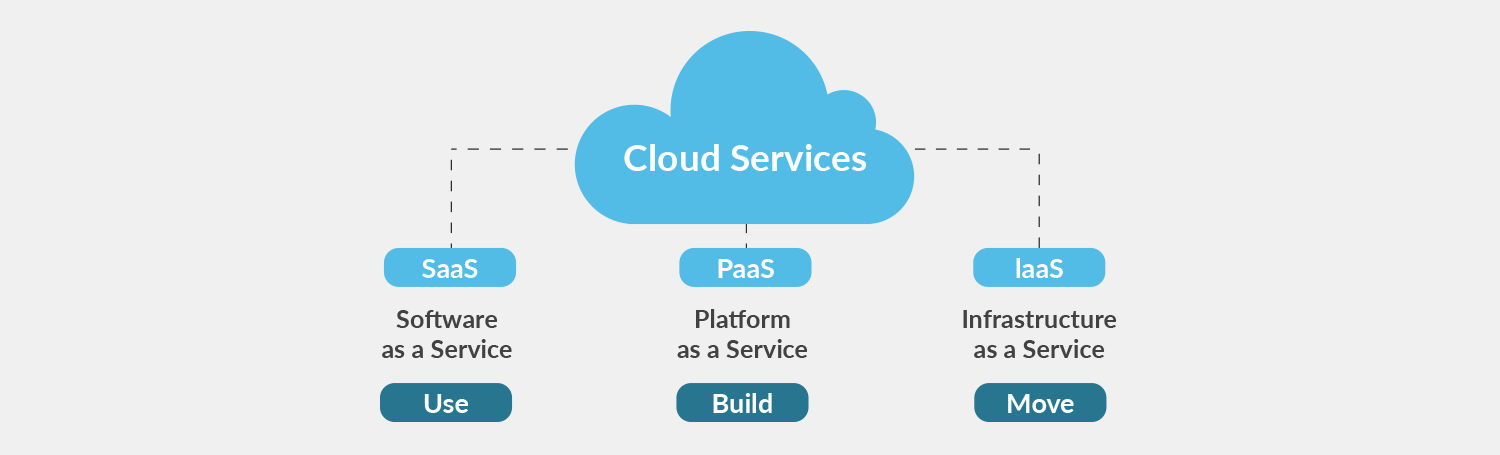
In verdict, leveraging cloud solutions for enhanced information safety and security is important for organizations to protect delicate information from unapproved access and possible breaches. By carrying out robust cloud protection protocols, consisting of data security, protected back-up solutions, gain access to controls, and compliance with policies, organizations can take advantage of advanced safety measures and expertise used by cloud company. This helps reduce threats efficiently and makes sure the discretion, integrity, and accessibility of information.

Data backup solutions play a critical role in ensuring the resilience and security of information in the occasion of unexpected incidents or information loss. By on a regular basis backing up data to secure cloud servers, companies can alleviate the dangers associated with information loss due to cyber-attacks, hardware failings, or human mistake.
Executing secure information backup remedies includes choosing trusted cloud solution companies that offer security, redundancy, and data honesty actions. By spending in protected data backup options, services can improve their information safety and security stance and reduce the impact of possible data violations or disruptions.